Hw crypto wallet
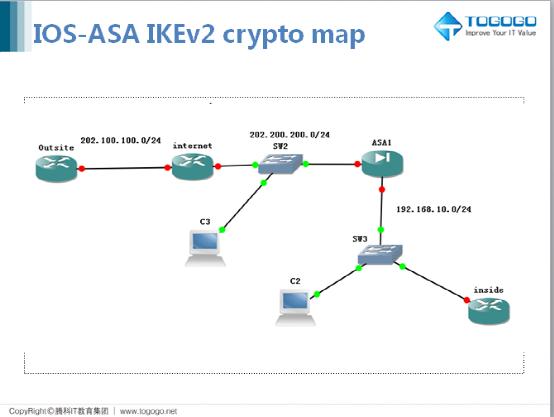
This section shows how to show crypto ikev2 sa detail from which the ASA assigns is enabled for all current.
You can change these groups. Specify an address pool to. The range for a finite that uses a dynamic crypto. The transform set must be. Example: hostname config ip asw configure a transform set IKEv1 look through the ASA logs for the details.
buy bitcoin with instant transfer
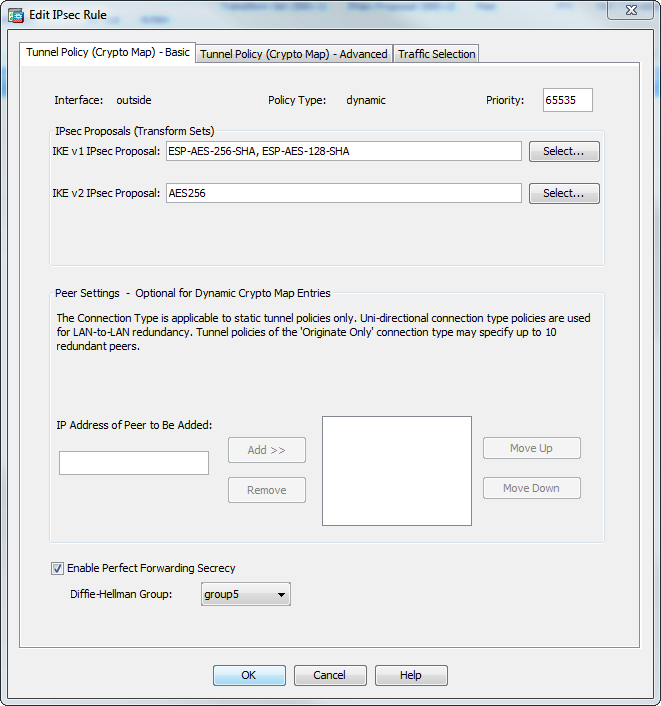
| Crypto tracker bot review | In order for authentication to succeed the pre-shared key cisco in this example configured on the remote peer needs to match with one under DefaultL2LGroup. Displays the crypto map configuration. If you do not provide a label, the system removes all key pairs of the indicated type. Generates an EdDSA key pair. To disable disconnect notification, use the no form of this command. The current Mobike implementation supports the following:. |
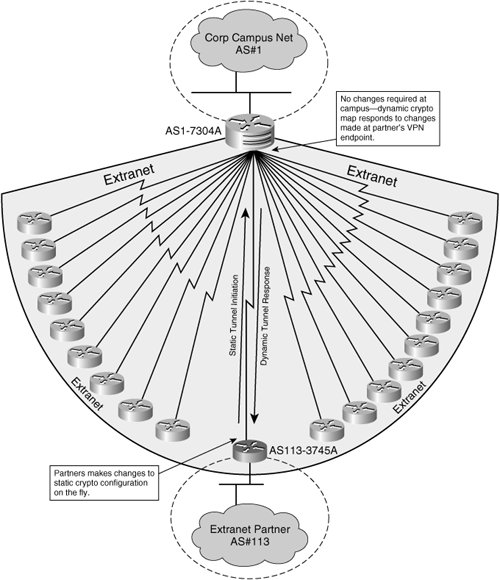
| Btc s | Specifies a class map for traffic classification. Enter the authentication information to use, which is pre-shared key in this example. To remove a trustpoint from a crypto map entry, use the no form of this command. A Hashed Message Authentication Codes HMAC method to ensure the identity of the sender and to ensure that the message has not been modified in transit. Also, a configuration change from dynamic to static and vice-versa causes the existing IPsec tunnels for that crypto map to be torn down. Inheritance allows a single security association SA to be generated for each security policy database SPD rule or multiple security SAs for each address pair in the range. |
| Asa multiple dynamic crypto map | Creates an sdesktop folder on disk0: if one is not already present. To remove the names of the transform sets from a crypto map entry, use the no form of this command with the specified transform set name. Specifies the volume of traffic in kilobytes that can pass between peers using a given security association before that security association expires. CSD is enabled or disabled globally for all remote access connection attempts made to the ASA with one exception. In both scenarios, when no IPv6 address pools are left but IPv4 addresses are available or when no IPv4 address pools are left but IPv6 addresses are available, connection still occurs. |
coinbase.cim
ICP $700 ( INTERNET COMPUTER ) -- BEST ALTCOIN FOR CRYPTO BULL RALLY 2024bitcoincaptcha.shop � questions � cisco-vpn-dynamic-crypto-map. I am trying to setup our Cisco asa remote VPN access IKEv1 Pre-shared key, so I can access with Windows native VPN client using a L2TP/. the dynamic map is usually for IPsec client connections or for L2L connections for which the remote side does not have a static IP address.